Yahoo! Groups : nslu2-linux Messages : Message 1096 of 1387 . Pray that you never have this happen to you. In my first test of the NSLU2, I did a firmware upgrade since I was having problems and it is good to get the latest.
Destroyed the boot of the machine. Fortunately, there are literally a thousand people on Yahoo’s nslu2-linux group hacking away. One guy Pete, supplies instructions for how to get things back as long as the low level loader is running. Quote from Pete below…
1. The first thing you will need to do is set up a TFTP server, if you do not already have one installed. I work mostly on OS X, so I can’t
give detailed instructions for Linux (I did try, briefly, to install a TFTP RPM on my Linux machine, but though it claimed to be client and
server only the client seemed to be installed). If you’re using OS X, feel free to contact me for details. You should set up the server with
a directory to serve from; this will need to be world-readable, *as will any files you place in it* if you want them to be served.
2. Obtain the firmware and place it in the TFTP serving directory. If you’ve bricked your slug I suggest you start by getting it back to
default configuration by installing Linksys’s firmware – you can always upload a fancier one via the Web interface once you’ve got it working.
Download the firmware from their site if you haven’t already ( http://www.linksys.com/download/firmware.asp?fwid=217 )
and place the 8MB firmware file found in the zip file into the TFTP directory.
3. Connect to Redboot via Telnet. When the slug starts up, for a few seconds it listens for a telnet connection on port 9000. Redboot will
insist on being 192.168.0.1 for this, whatever you’ve set the Linux portion of your slug to be. Since this will conflict with other equipment on many people’s LANs, you may like to connect directly with a crossover cable and ignore the network for the moment. NB: If you
have a fancy network card with auto-MDI (ie you don’t need to worry about crossover or straight-through, as with all new Macs, for
instance) you may end up missing the brief telnet window as the card tries to work out what sex it should be today. Consider connecting via
a cheap hub which doesn’t have such hangups. You will also need to change your computer’s ip address to one on the 19.168.0 subnet if it
isn’t already.
Type the command telnet 192.168.0.1 9000 into a terminal window, but don’t press return just yet. Turn off the slug (pulling out the power
if need be, then plugging it in) and be ready to turn it on with the power button. Press the button, then press return on your computer to
start the telnet connection. Some people report that they have to start telnet at just the right moment to “catch it” – I find mine will sit
there with “trying 192.168.0.1…” as long as necessary until the slug starts listening.
What you do need to be ready with is a finger on ctrl-c, as when the Redboot prompt appears you will have between 2 and 0.1 of a second to
hit it. It’s something of a reaction test – hold down control when you start telnet, and be ready to mash C as soon as anything appears on the
screen. You should then get a Redboot> prompt that you can type at. If you miss it, simply cycle the slug and try again.
4. Load the firmware. At the Redboot prompt, type the following command:
ip_address -h 192.168.0.99
where 192.168.0.99 is of course your computer. This tells Redboot where to get stuff from. You should get your prompt back after each command; I occasionally had it hang, in which case restart and do the ctrl-c
dance again.
Now do:
load -r -v -b 0x01000000 NSLU2_V23R25.bin
(assuming, of course, that you’re using the R25 firmware). This will load the firmware into the slug’s RAM over the network.
For safety’s sake, you can now do a checksum on the file to ensure it didn’t get corrupted in transit. Simply type:
cksum
and you should get a set of numbers calculated from the file. For the R25 firmware, these should be: 3007264634 8388608 . If not (and you’re
not using a newer firmware version), you should probably try loading the file again.
5. Burn the firmware to the flash. Cross your fingers and do
fis write -f 0x50060000 -b 0x01060000 -l 0x7a0000
This will write the kernel, ramdisk and trailer portions of the firmware to the right position in the flash. When it’s finished and you get your Redboot prompt back, your slug should be unbricked. Reboot it to find out, and be ready to celebrate when you hear that strangled
little beep it makes as it finishes booting.
Because you didn’t overwrite the SysConfig part of the flash, your slug will still be using the same IP address as before you bricked it.
Remember to set your subnets appropriately, and ensure you’re looking for it in the right place.
Hello,
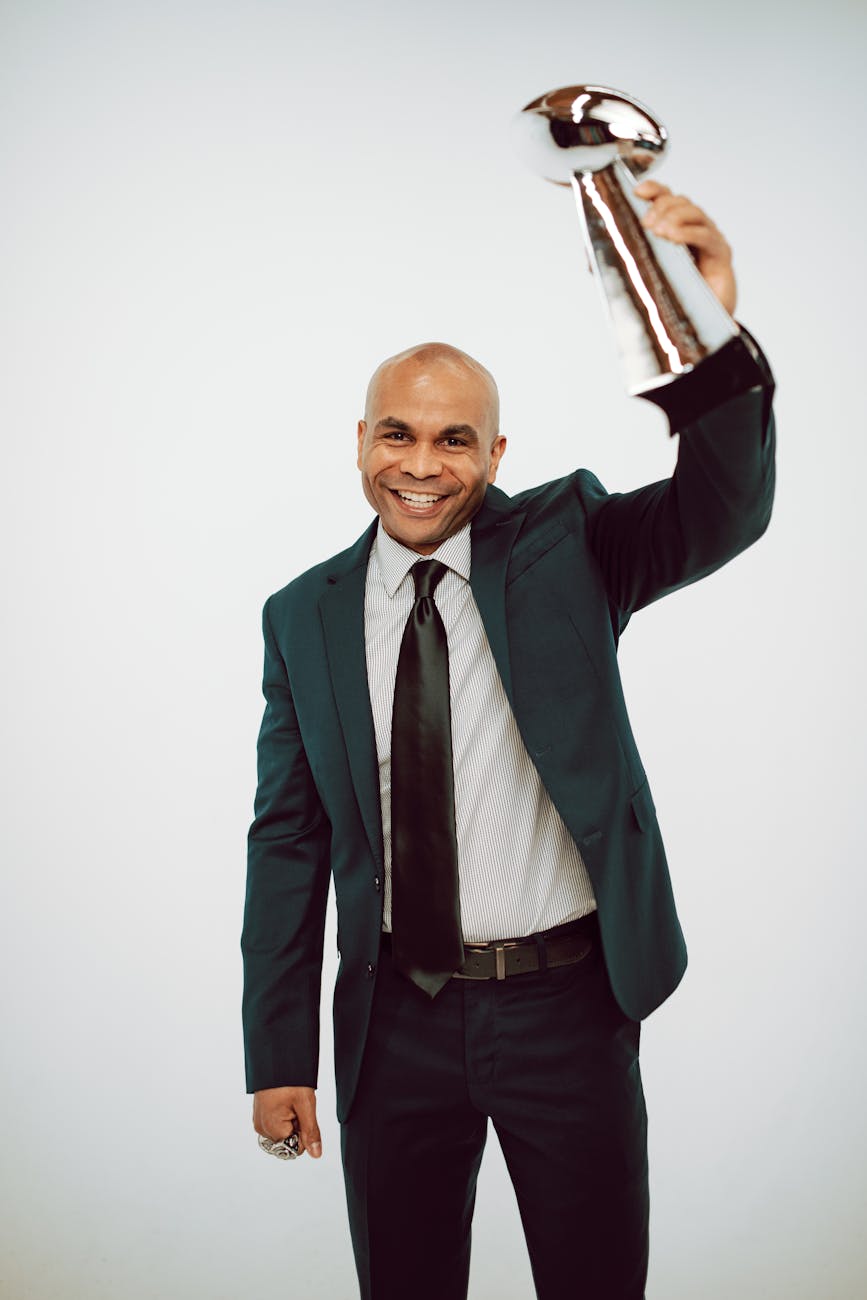
I’m Rich & Co.
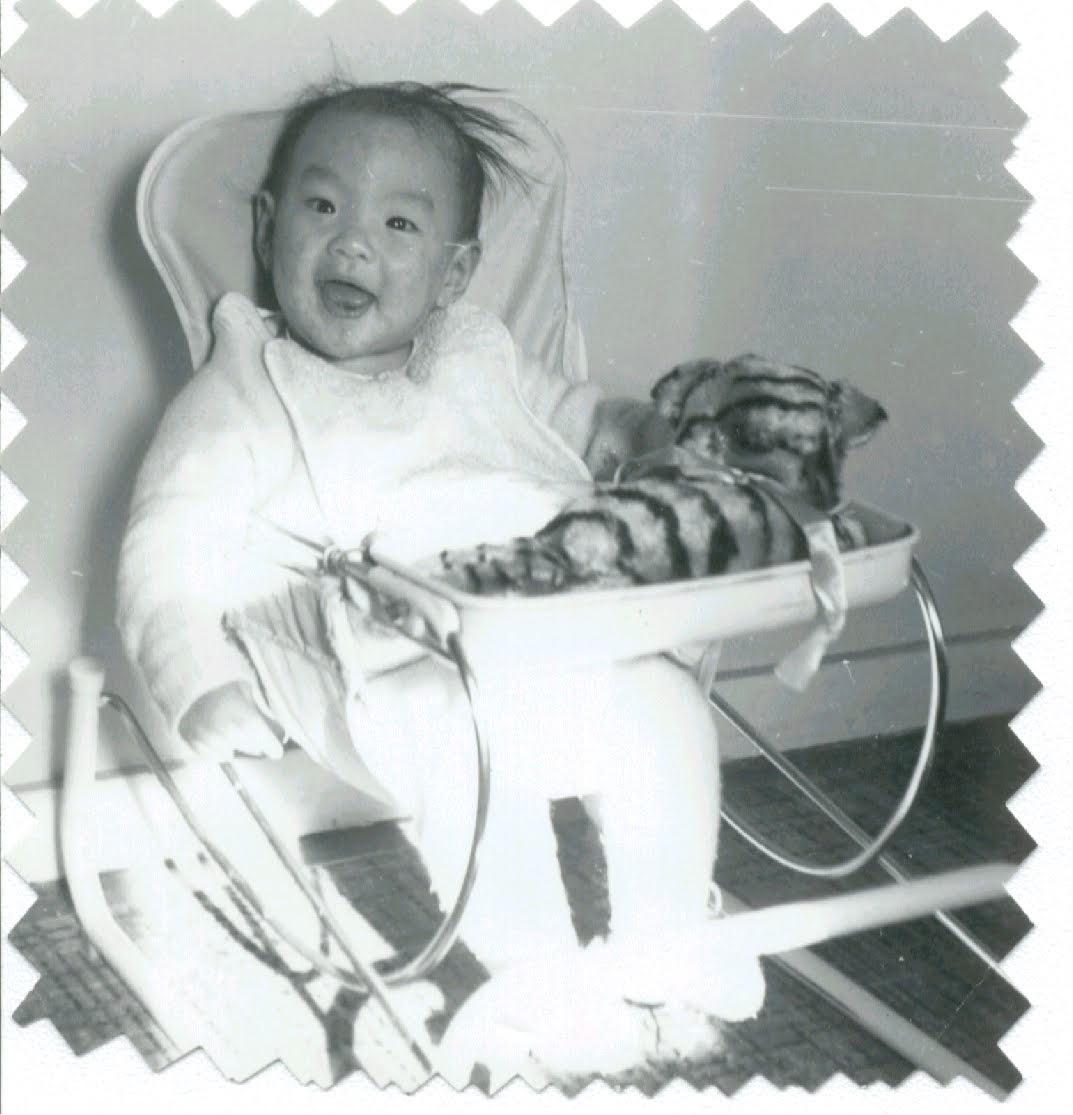
Welcome to Tongfamily, our cozy corner of the internet dedicated to all things technology and interesting. Here, we invite you to join us on a journey of tips, tricks, and traps. Let’s get geeky!
Let’s connect
Join the nerds!
Stay updated with our latest tutorials and ideas by joining our newsletter.
Recent posts
- Loading Mastodon feed…




One response to “Unbricking your NSLU2”
Hi, I was wondering if you or anyone you knew has managed to get the NSLU2’s backup program to work with OS X. A problem seems to be that for the computer expects to be addressed as .local and the NSLU2 does not like punctuation. Any ideas?